You’ve probably been asked many times to help a family member or a friend with a computer problem. You give in, knowing that helping them won’t take that long (hopefully), but you are doing your part as a cybersecurity professional.
After all, you’ve clocked over thousands of hours in cyber training – How hard can this be? The cyber definitions, concepts and practical implementation are like second nature to you. As you get to listen to the problem at hand, you start formulating a plan to fix the problem. This involves listening to the explanation of “the problem” … “computer is running slow”, “it takes a long time for the application to open”, “browser closes without reason”, etc.
As any cyber sleuth would, you start with the most basic question: “When was the last time you updated the OS and the applications experiencing issues?” and just like you expected, the answer is oftentimes:
“Updates? What updates?”
“Was I supposed to update something?”
“We just purchased the McAfee 3yr license to take care everything. We didn’t know we had to do something.”

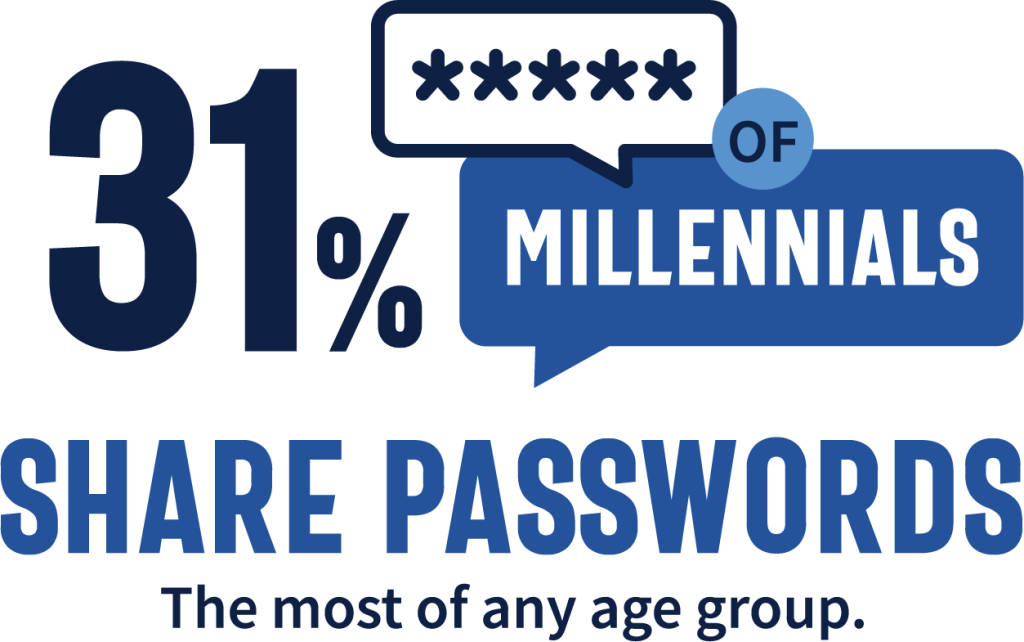
If the laptop hasn’t been updated since it was purchased, it is safe to say none of the latest critical patches have been installed. The best path forward is to check for system updates and get it configured immediately to download the patches ASAP. As suspected, it will take a couple of hours and multiple reboots to complete the update. It’s getting late, you’ve had dinner, watched a movie and the laptop is still updating but you’ve got to go. You leave detailed instructions to complete the update before anything else is done on the laptop including changing the default passwords. Everyone agrees they’ll do a better job to keep up with patches and they won’t share the passwords anymore.
It’s been a couple of weeks since the laptop patch update incident, so you do a follow up to see how everything is going. Lo and behold, you find out that the problems are still happening. You ask to confirm if the patch installation completed and no outstanding updates are pending… again you get an answer that’s not what you wanted to hear: “The last patch rebooted the computer and kept showing a percent on the blue screen of the patch install, but it never completed. It just got stuck there so we decided to shut down the computer to see if it would fix it. It worked, and we could log back in.”
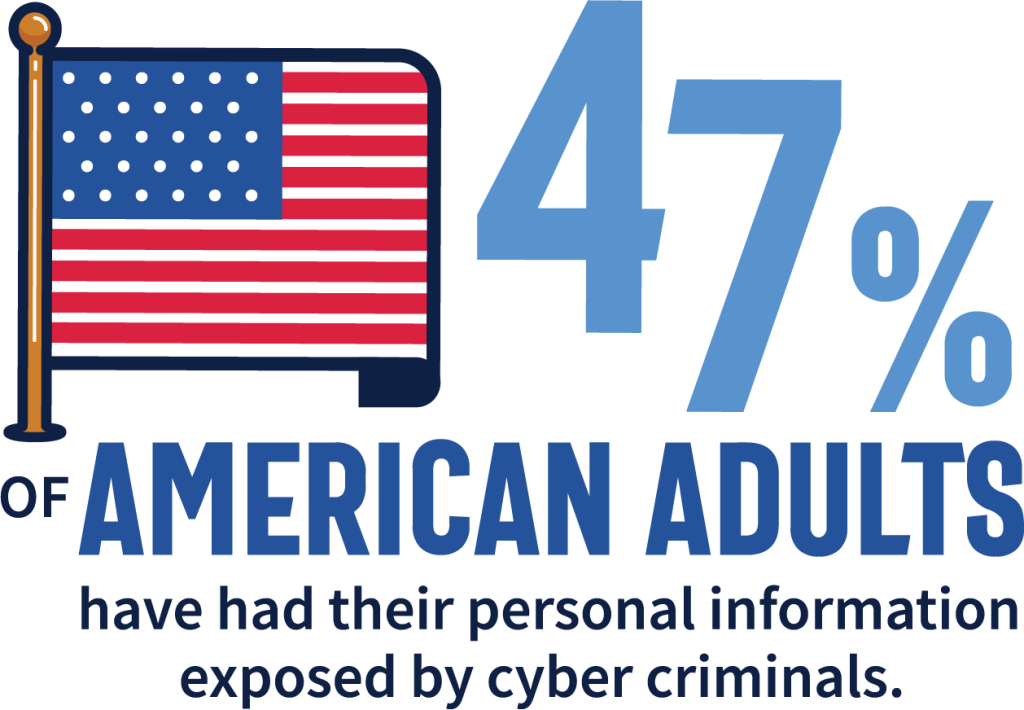
But you know better, instead of finishing the patch install, the reboot aborted the update, leaving the laptop in the same vulnerable state as before. Now, they share that they are having other problems with their online accounts which hadn’t happened before.
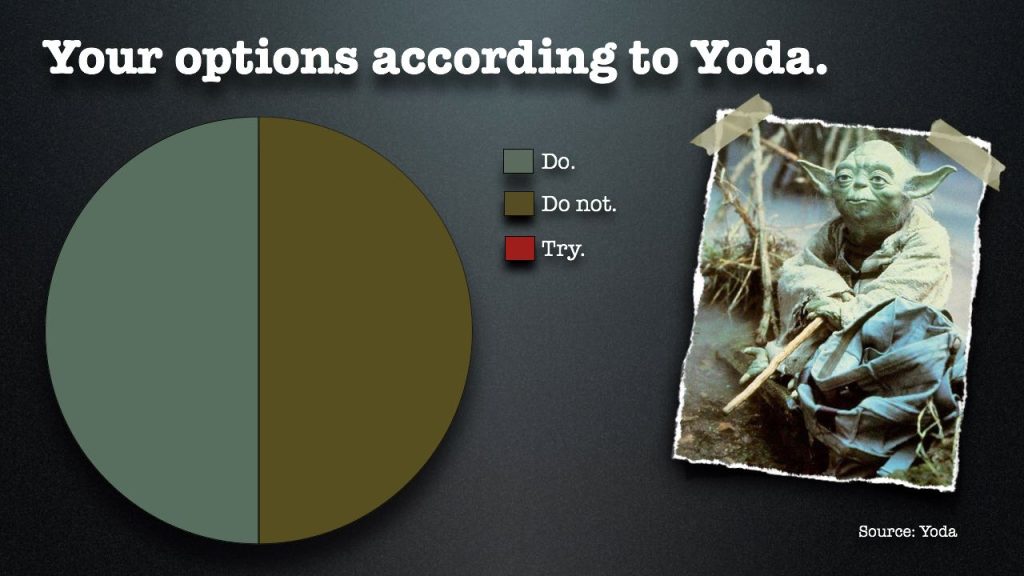
Although you are ready to don your Cyber Jedi Master robes and teach these young Padawan’s the way of the Cyber SME, you reconsider as your previous attempts to get them to do the “right thing” didn’t work….It’s time for a new approach to make them Cyber Smart.
Here are a few discussion topic ideas:
- Talk about protecting the laptop’s security and passwords by comparing it to their car, which is full of family gifts, parked in the mall parking lot over the holidays.
- Bring up topics such as not posting on social media accounts when they are traveling on vacation (oversharing & geotagging) – You wouldn’t post a banner in front of your home informing the entire neighborhood (and, by association, burglars) when you’re out, so don’t do the same on social media.
- Ask them if they would you call the 1-800 number on the junk mail postcard letting you know you won a special prize? Likely not – just like you shouldn’t click embedded links in emails that you get even from someone you know, unless you check with them via a different means (separate email, text, or call) to make sure they sent the message.
- Lastly, scams are plentiful, so break them down in simple terms:
- Phishing attacks – They want you to reply to a staged urgent message to retrieve your information. Government agencies and credit card companies don’t typically use phones as a way of communication – always question the source before giving away your information.
- Imposter scams – The prince isn’t really trying to give you money.
- “You’ve won” scams – If you didn’t play the game, you didn’t win.
- Healthcare scams – There are privacy laws to protect personal health information (PHI), so don’t discuss it over the phone unless you called your healthcare provider.
- Tech support scams – Microsoft has no interest in connecting to your computer to see if it is running slow.
Do you have ideas on how to share Cyber Smart ideas with non-IT/cyber people you know? Would love to hear your approach to making us Cyber Smart without being a Cyber Smart Aleck.